All About SSL: What It Is, How It Works, Types, & More
 Fact-checked
Fact-checked
Last Updated: February 1, 2023
Sensitive data you share with trusted parties on the internet should be carefully protected with encryption algorithms. Secure Sockets Layer (SSL) is a cryptographic protocol used to provide security to data transferred between a web browser and a server. But how does SSL work? This article addresses what an SSL is, how it protects your data, the benefits of using it, and how to recognize a non-protected connection.
What Is SSL/TLS
Secure Sockets Layer (SSL)—or Transport Layer Security (TLS)—is an encryption protocol that provides secure ways of communication on the internet. It disables third parties to intercept and read your data by making them understandable only to the intended recipient.
SSL can be used for remote logins, emails, websites, and much more, including intranet connections. Often, the two parties communicating are a server and client, but sometimes encryption is essential in server-to-server and client-to-client communication.
What does SSL stand for compared to TLS? SSL is the term used for earlier versions of this cryptographic protocol, which was replaced with Transport Layer Security (TLS). But many still use the term SSL.
| NOTE: The first version of SSL, in the 90s, was never released due to security issues. Years of research resulted in the technology that makes internet transactions as safe as they can be. |
How Does SSL Work?
Secure Sockets Layer (SSL) enables a secure channel of client-server communication online by using encryption and decryption methods to make sure the message is safe while in transit.
SSL generates a public key and a private key to perform this function, used for encrypting and decrypting the data, respectively, and making them readable again. Without the appropriate key, you wouldn’t be able to read the message, which means that the information is safe from any intruders looking to intercept and steal sensitive data.
You can realize how SSL works by envisioning a padlock and key combination—a padlock to lock the door (encrypting the message) and an appropriate key to unlock it.
It’s easy to spot the difference between non-secure and secure connections. With secure connections, the URL starts with Hypertext Transfer Protocols (HTTPS). When websites don’t have SSL/TLS protection, their address begins with HTTP.
You shouldn’t use the HTTP addresses for sending any confidential information. Once intercepted, it will be readable and available for third parties.
| NOTE: Many browsers warn that a connection is not secure, usually displayed in red fonts before the site’s address. Those addresses start with ‘http://’ instead of ‘https://.’ |
Types of SSL/TLS Certificates
SSL certificates—an essential element of secure connections—have two main functions: authentication (verification) and data encryption. These certificates, issued by the Certificate Authority (CA), work on a Transmission Control Protocol (TCP) based on a combination of asymmetric and symmetric cryptography that provides secure channels for online communication.
An SSL certificate issued by a respected CA results in a higher level of trust by partners, clients, and customers. Although all SSL certificates provide a data encryption process, there are differences in certifications available and identity verification standards.
Understanding SSL certificates requires knowledge about their three primary differences, seen below.
1. Extended Validation (EV) Certificates
EV certificates are the most trusted SSL certificates. To obtain an EV certificate, a company must go through a detailed and globally standardized process, providing proof of its operational, legal, and physical existence, its exclusive right over the domain, and the entity’s authorization of the issuance of the certificate.
The extensive information about the company’s identity is included in the Secure Sockets Layer (SSL) certificate. This TLS certificate requires more time and money for the company, but it provides a higher level of data integrity and trust by clients, customers, and partners.
2. Organization Validated (OV) Certificates
The CA issues OV certificates for legally registered companies that prove their ownership over the domain they want to secure. They require more identity verification steps for the SSL process of issuance than DV certificates but less than EV certificates.
With OV certificates, you can find identity information about the company by clicking the gray padlock in the web address bar of your browser, which is not the case with DV certificates.
3. Domain Validated (DV) Certificates
The process of issuing this type of certificate is mainly automated. It doesn’t provide additional security regarding the company’s identity—other than the confirmation that the person wanting to secure the domain has administrative control over it.
DV certificates don’t contain any information in the company name field that would help you identify the company behind the domain. Although this certificate ensures that the information sent is encrypted by the SSL protocol, it doesn’t provide the information to whom the data is being sent—other than the domain owner.
DV certificates are not recommended for e-commerce companies or websites with options for internet transactions because of the easy and low-cost process to get them—fraudulent companies often obtain them.
| NOTE: In the past, you could quickly spot the websites with EV certificates by the website name displayed in the browser in green fonts or on the green bar with the name and location of the company that owned the certificate. Dominant browsers (Mozilla Firefox, Google Chrome, etc.) removed this distinction in 2019 and now display a grey padlock in the address bar for all types of SSL certificates. |
Key Takeaways
| SSL is an encryption protocol used for the protection of sensitive data exchanged online. |
| Depending on how an SSL certificate works, there are three types of SSL certificates for owner verification with different criteria for issuance. |
| TLS is the new name of SSL. |
| Secure connections begin with an SSL/TLS handshake, and the address of websites starts with HTTPS. |
TLS/SSL Handshake Protocol
TLS handshake is an asymmetric cryptography process that is used to establish a secure client-server connection. Each HTTPS connection starts with this process, but how does SSL handshake work?
The encryption and decryption process is performed by using a set of keys. An RSA key exchange algorithm is one of the oft-used asymmetric encryption algorithms. Note a nine-step explanation of an SSL handshake when a Rivest–Shamir–Adleman (RSA) algorithm is used:
Client Hello
Upon building a Transmission Control Protocol (TCP) connection, the client sends information to the server (SSL version, compression method, cipher suites).
Server Hello
The server then identifies the highest version of SSL that they both support, chooses the compression method and cipher suites from the client’s options, and sends a copy of its SSL certificate (a public key).
SSL Authentication Process
The client verifies the SSL certificate sent by the server. Once it determines that it’s trusted, the client moves on to the next step.
Premaster Secret
The client sends a ‘premaster secret’—a random string of bytes encrypted with the public key that was sent by the server and can only be decrypted with a private key.
The Decryption of Premaster Secret
The server decrypts the message received by using its private key.
Session Keys Creation
Both client and server generate session keys using server and client random and premaster secret.
Client Is Ready
The client sends a finished message encrypted with the session key.
Server Is Ready
The server also sends a finished message encrypted with the session key.
Secure Symmetric Encryption Achieved Through SSL Algorithm
After these steps, a secure connection is established, and the communication continues using the session keys.
Not all TLS handshakes use a private key when generating session keys. Some kinds of handshakes slightly differ in the listed steps—the server may use its digital signature to verify that it has a private key that matches the public key from the SSL certificate.
| NOTE: The SSL handshake is wholly automated without any inconvenience or delay for the user. But if the handshake process isn’t successful, the connection will end, and the user will receive a warning message from its browser, which can make a difference between what is an SSL connection and what isn’t. |
Using SSL Certificates
Initially intended for the World Wide Web, SSL certificates are the golden standard in internet data protection, widely used in enterprises to secure different types of internal and external connections.
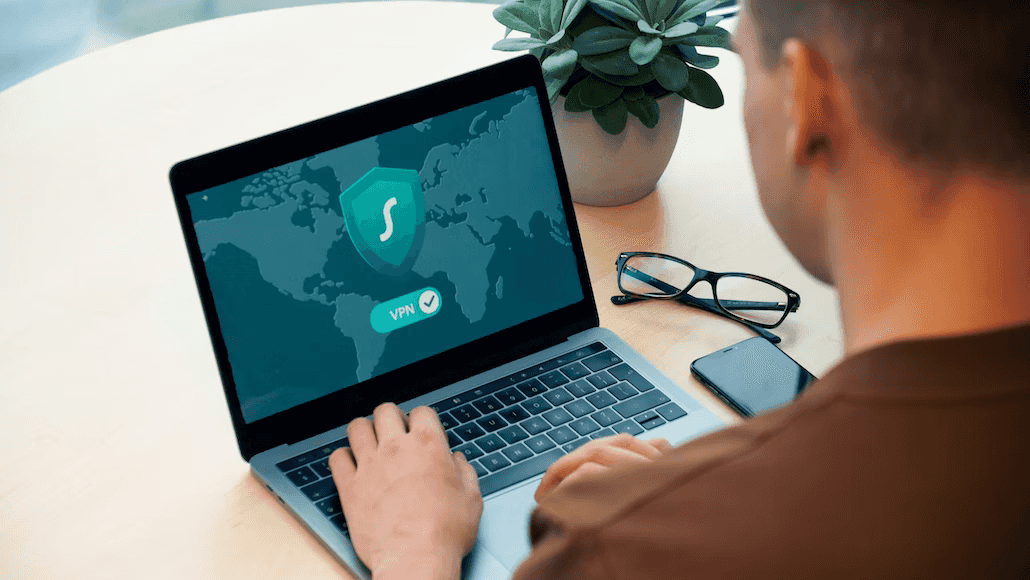
SSL can also be used in emails, Network Access controls, Internet of Things (IoT), Single sign-on (SSO), and Virtual Private Networks (VPN). To make the most of this type of connection, check some of the top VPNs out there.
How does SSL certificate work in regards to business benefits? Note four advantages of SSL certificates for businesses:
1. Higher Level of Trust
Owning an SSL certificate will allow your clients and partners to be more confident about your identity and feel safe about the information they want to send you.
2. Higher Engagement Rate and Number of Transactions
It’s unlikely that a client will cooperate with a company if facing a warning message on their browser when trying to connect with a site. Additionally, if your company uses online payment methods, the lack of an SSL certificate can be a substantial setback.
3. Better Website Ranking and Visibility
Google introduced SSL communication with a warning message if a website doesn’t have an SSL certificate. Sites with SSL certificates have higher ranking positions in search results, making it easier for your clients to find you.
4. Lower Risk of Data Protection Breaches
To make it significantly difficult for malicious parties to intercept your data, the best you can do is know how SSL certificate works and obtain one. Even if the data is stolen—due to encryption—the message won’t be understandable without the appropriate key.
| NOTE: Ecommerce statistics show a significant increase in online shopping—as well as fraudulent activity—due to the COVID-19 pandemic. Therefore, it’s crucial to know how to protect yourself, considering the consequences of unauthorized usage of personal information. Because advanced methods are not easy to recognize, you should consider some of the top identity theft protection companies. |
Conclusion
How does SSL work? Keeping your data safe and your company’s reputation intact is essential in today’s business world. An SSL certificate will provide you with the necessary protection and give additional credibility to your business.
FAQ
Both acronyms stand for the same thing—an encryption protocol used for securing data online. TLS is a newer version that has replaced SSL. The terms, however, are used interchangeably.
The encryption methods used for data protection while in transit are considered safe. Depending on the SSL certificate that the website owns, identity verification is more or less reliable.
SSL is used for creating a secure channel of client-server communication and for the protection of information exchanged online. But how does SSL work? It uses decryption and encryption methods utilized in enterprises for different types of external and internal data protection and client-to-client or server-to-server communication.




![How to Find Someone’s Tinder Profile? [2024 Expert Guide]](https://review42.com/wp-content/uploads/2023/06/Finding-Someone-on-Tinder.jpg)